Data Center

Modern Storage The Answer to Multicloud Complexity
No matter what it's called or how it's described, it's a serious problem that's only getting worse. As...
The top 3 benefits of predictive intelligence in service operations
The demand for better, faster, cheaper and more scalable IT services and operations has never been greater....

Get Closer in 2021: Key Trends from NRF
Another by-product of 2020 is the digital transformation that is happening within the retail industry....
The Top Five Reasons to Choose Toad Over SQL Developer
Now that DevOps initiatives are becoming the norm, you're under increasing pressure to deploy application...

Achieving Data Excellence in Financial Information Management
Financial institutions have accumulated large quantities of valuable data and metadata, but the levels...

The Forrester Wave™: Big Data NoSQL
In this report, Forrester states that, 'NoSQL has become critical for all businesses to support modern...

SME Lending: The Road to Real- Time Approvals
How to Build World-Class SME Lending Experiences Thirty-two percent of SMEs now work with online lenders...

Three reasons to manage Office 365 with Citrix Workspace
Are you considering migrating to Microsoft Office 365 or already facing challenges with the move? Don't...

The CIO's Guide to Cloud Data Management
Data is power. How you use it and how you protect it is critical. As a CIO, you are responsible for leading...
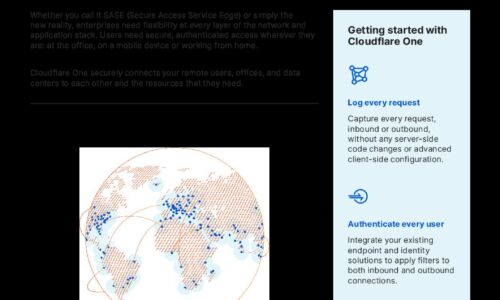
Cloudflare One
Cloudflare One is a network-as-a-service solution that simplifies and secures corporate networking for...

Forrester: The Balanced Security Imperative
Balanced security requires firms to transition from treating privacy and data security as compliance...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.







