Data Center
An Integrated Approach to Embedding Security into DevOps
Organizations are adopting DevOps as a development and operational model to facilitate the practice of...
Zero Trust Access for Dummies
As businesses continue to embrace digital innovation, cloud applications, and the new work-from-anywhere...

Successful Microsoft Azure Migration with Quest Data Empowerment Tools
What if there was a model for methodically approaching migration of even your most entrenched relational...

5 Best Practices for Securing Modern Web Applications and APIs
Web applications are nothing new. Neither is web application security. Many businesses have been building...

Practical Guide To A Zero Trust Implementation
Zero Trust is becoming the security model of choice for enterprises and governments alike. However, security...

Powering Digital Transformation with a Hybrid Cloud Strategy
It's not news that companies in every industry are fundamentally transforming the way they do business. Scrappy...

CISSP For Dummies
Secure your CISSP certification! If you're a security professional seeking your CISSP certification,...

Understanding the Obstacles to WAN Transformation
Network engineering and operations leaders are looking to software-defined wide area networks (SD-WAN)...
Common Browser Isolation Challenges and How to Overcome Them
Every security team wants to keep their employees and data safe from the latest threats. To accomplish...
Dell Technologies Continuously Modern Storage Whitepaper
Modernize Data storage to Accelerate Operations and Digital Business Initiatives. Learn more about Dell...
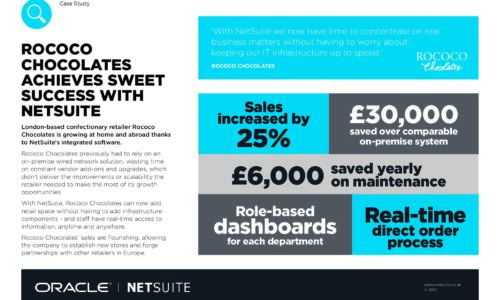
Rococo chocolates achieves sweet success with NetSuite
London-based confectionary retailer Rococo Chocolates is growing at home and abroad thanks to NetSuite's...

20 Examples of Smart Cloud Security
Smart cloud security provides critical capabilities such as governing access and activities in sanctioned...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.