Data Center
A Public Sector Guide to Getting More From IT
The Covid-19 global pandemic has had a huge impact on organisations of every size and in every sector,...

Future Proof your Investment Strategy for Data Center and Cloud
Today's organizations are under more pressure than ever to innovate fast and offer a superior experience...
Privilege Access Management Buyers' Guide
Security breaches show no signs of slowing, and credential theft is the number one attack vector. Privileged...

Securely Work From Anywhere With the Fortinet Security Fabric
The way people work has fundamentally evolved, and organizations need to be able to keep workers productive...

Building the Business Case for Improving Endpoint Security
As a security provider, we understand that convincing executives to make changes to their stack can be...

Trends in Hybrid Cloud
Cloud computing has helped many enterprises transform their IT practices over the past five years, but...

IDC: Strategies for Building Digital Infrastructure Resiliency
Multiple generations of applications. Multiple generations of infrastructure. Is there a way to reduce...
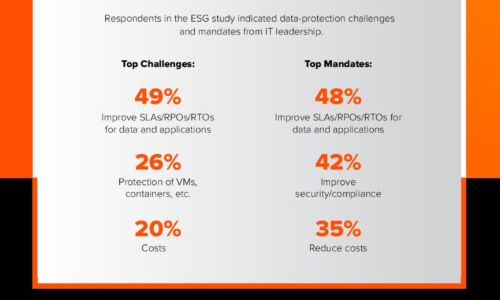
Close the Data Availability Gap
A recent ESG survey of over 1,000 global IT decision-makers found that 82% of enterprises are facing...

G2 Mid-Market Endpoint Protection Suites Report
Thinking about investing in endpoint protection and want to get a real sense of how different solutions...

Public Sector Cloud Journey
As the government continues to move workloads to the cloud, many agencies are struggling to automate...

Application Control for Dummies
Application control, sometimes called application whitelisting,is a means for controlling the software...

Replace AV Buyer’s Guide
Today's businesses face a unique set of security challenges. Many organizations know their current antivirus...
How To Choose a Managed Extended Detection and Response Solution
Organizations face major cybersecurity hurdles. The first challenge is finding effective cybersecurity...

Forrester Consulting Study: Trusting Zero Trust
The growth of ransomware and work-from-anywhere employment has created vastly greater security risks....
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.




