Data Center
Challenging Times Call for a Cybersecurity Plan of Action
Could there be a more 'exciting' time to be a cybersecurity executive? Some might choose other adjectives:...

Security Starts Here - Privileged Access Management
The need to support safe and secure remote access for administrators, high-profile breaches (SolarWinds,...

The Economics of Cloud Options in Government
Through the lens of Cloud Economics, explore the risks and benefits of the three ways to upgrade and...
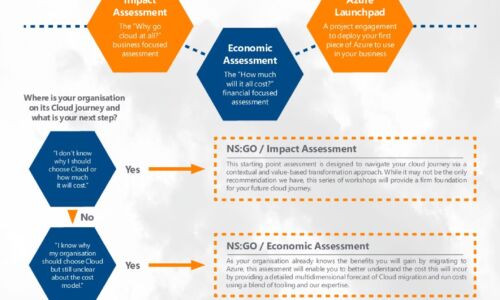
Azure Accelerator kit: Travel in the fast lane with New Signature
At New Signature, we understand that organisations are finding it difficult to start their Public Cloud...

Top 4 Pitfalls to Avoid when Deploying Office 365
There's no denying that Office 365 is a big deal. It's a big part of the Microsoft Intelligent Cloud...

Top 10 Active Directory Security Reports and Alerts You Need
Traditional perimeter defense is simply no longer good enough. Today, identity is the new perimeter —...

G2 Mid-Market Endpoint Protection Suites Report
Thinking about investing in endpoint protection and want to get a real sense of how different solutions...

You've Got BEC!
A Roundup of the 10 Biggest, Boldest, and Most Brazen Business Email Compromise Scams of 2020 and 2019. It's...

Keeping Critical Patients Safe and Treated Using SD-WAN
MD Anderson Cancer Center leveraged VMware SD-WAN to help radiologists be more productive, and staff...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.