Latest Whitepapers

Take Control of your Office 365 Data
This short, easy-to-read analyst report by 451 Research provides their view on the importance of backing...

Aligning Cyber Skills To The NICE Cybersecurity Workforce Framework
NICE stands for national initiative for cybersecurity education It is a partnership between government,...
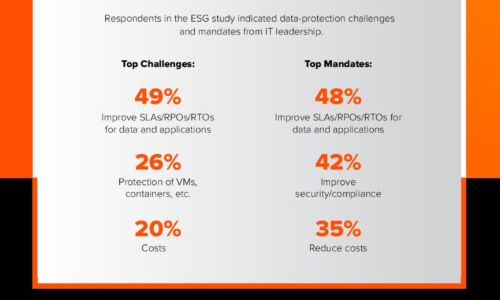
Close the Data Availability Gap
A recent ESG survey of over 1,000 global IT decision-makers found that 82% of enterprises are facing...

PerimeterX is named a leader in Bot Management by Forrester
PerimeterX was named a leader in The Forrester New Wave™: Bot Management, Q1 2020. According to the...
How to Get and Maintain Control of Your Microservices
Learn how a hybrid application delivery system powered by Citrix ADC can help you gain control of your...

Network Security that sets the standard for local government
When it comes to network security, organisations can — and must — learn from the experiences of others....
IT Service Management for SMBs in a Remote-First World
Let's start by defining the term IT Service Management or ITSM. Basically, it's everything involving...

5 signs your SaaS company needs to improve its usage data management
If your SaaS company offers usage-based pricing, there's a good chance you've built an in-house solution...
Absence Management: The Last Easy Money for Retailers
One of the many challenges facing retailers today is their ability to adapt quickly to a rapidly changing...

How to Meet Digital Expectations in IT: A European Study
More than 4,000 customers have told they us they want to go digital, while 800 senior decision makers...
Building Sustainability into the Modern Business Landscape
The modern business landscape requires a new focus on climate responsibilities. 2020 and 2021 will be...
Edge to Cloud eBook
When it comes to security, enterprises must be increasingly agile—especially as the threat landscape...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.