Latest Whitepapers

Managing Sprawl in Microsoft 365
How content sprawl happens, why it matters, and steps every IT leader should take to avoid it. Sprawl...

The Best of Both Worlds: Hybrid IAM Offers Flexibility and Enhanced Security
One of the fastest growing segments of the Identity and Access Management (IAM) market is the cloud segment. Increasingly,...
Top Seven Reports for Supporting a Growing Virtual Workforce
IT environments are more dynamic than ever, and having more users working from home introduces new vulnerabilities....

The Digital Workspace: Three Elements of Success
IT leaders say they are actively pursuing digital workspace strategies but still need to overcome some...
Redefining Modern Master Data Management in the Cloud
Your organization needs to continuously innovate to stay competitive. And business insights are necessary...
Inherent Vulnerabilities Harming Telecommunications Companies
Telecommunications companies are among the most targeted companies in the world, attracting the most...
Cloud is an Operating Model, Not a Destination
The cloud is not simply a destination for workload migration that also somehow solves IT operational...
Challenging Times Call for a Cybersecurity Plan of Action
Could there be a more 'exciting' time to be a cybersecurity executive? Some might choose other adjectives:...

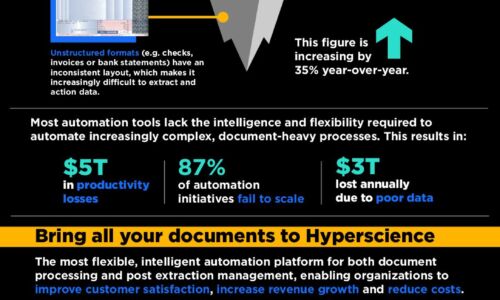
Set your document data free
Escape from manual document processing and find freedom in a machine learning solution. Work more efficiently...

Public Sector Cloud Journey
As the government continues to move workloads to the cloud, many agencies are struggling to automate...

Change management blueprint for contact centre digital transformation
The COVID-19 pandemic put organisational change into hyperdrive. Businesses were compelled to move to...

Work from anywhere - Empowering the future of work
Almost overnight, nearly every organization around the world had to mobilize their workforce to operate...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.