Spam

Stopping BEC and EAC
Business email compromise (BEC) and email account compromise (EAC) are complex problems that require...

The Zero Trust Guide To Remote Worker Security
With the recent increase in the number of employees working from home as a result of the COVID-19 outbreak,...
The New Era of Fraud: An Automated Threat
Fraudsters employ bots and automated attacks that scour apps looking for any opportunity to hijack business...
Cyberthreats: A 20-Year Retrospective
Annual threat reports provide an opportunity to look back at significant events of the past 12 months...
2021 Email Threat Report: It Started Out With a Phish
Our 2021 Email Threat Report analyzes the top threats seen over a period of a year across organizations...

A Guide for SMBs: Can I really become 'less hackable'?
After nearly 20 years working in cybersecurity, I am still asked the age-old question by business owners:...

13 Email Threat Types To Know About Right Now
Traditional email security doesn't cut it anymore. In today's rapidly evolving environment, traditional...

Best Practice Makes Perfect: Malware Response in The New Normal
Before Covid-19, cyber security teams already confessed to being overworked – as high-profile security...
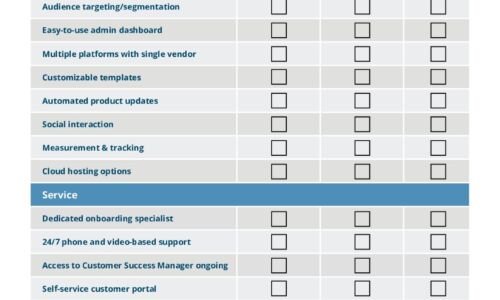
IT Comms Plan Bundle
IT teams need to communicate important messages across their organization – from scheduled maintenance...
Cybercrime tactics and techniques
2019 is off to an action-packed start in cybercrime. From a steadfast increase of pervasive Trojans to...
PHP, MySQL, & JavaScript All-in-One For Dummies
Get the basics on four key web programming tools in one great book! PHP, JavaScript, and HTML5 are essential...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.