ERP
Future-Proof your Organization’s ERP System
Organizations need a clean core for transformation and future-proofing their ERP investment. No matter...
Growing the Factory of the Future
To transform manufacturing, transform the workforce. Digital transformation – a key element of what's...
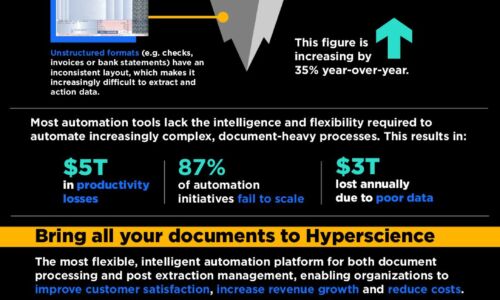
How to Save Millions for the New Tomorrow
A guide to finding savings with mission-critical solutions that pay for themselves in months.In today's...

Powering Dynamic Personalization with Data
With so much data available, and advanced tools at our fingertips, it's possible to create dynamic, 360-degree...
Hybrid Work: Why it's time to move your on-premises PBX to the cloud
For years, the shift to cloud-based communications services was gradual, with some organizations going...

Enrich the Client Experience with VMware Edge Network Intelligence
An AIOps solution for a distributed and secure workplace. Ensures end user and IoT client performance,...
How to Get and Maintain Control of Your Microservices
Learn how a hybrid application delivery system powered by Citrix ADC can help you gain control of your...

How Treating Data as a Strategic Asset Drives Growth
This IDG eBook explores how organizations can build a successful and sustainable data approach to capitalize...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.