Cloud Computing
Transforming the SOC: Building Tomorrow’s Security Operations, Today
When you think of a security operations center (SOC), what comes to mind? Is it an organized team of...

Sprinting Ahead With Agile Auditing
Internal auditors must be nimble to navigate today's complex business world, where they're expected to...
How to Stop Business Email Compromise Threats
While staggering ransomware demands tend to hog the headlines, Business Email Compromise (BEC) is one...

Proofpoint Security Awareness Training
Proofpoint Security Awareness Training Enterprise helps you deliver the right training to the right people...

A Unified Workspace delivers a transformative employee experience
A critical business edge comes from employees who are engaged, inspired and happy–thanks to the right...
Managing the Cybersecurity Skills Shortage
The cybersecurity skills shortage has grown more urgent in recent months amid 'The Great Resignation'...

Supply Chain Security Is Tough: So What Should Good Look Like?
Managing and securing software supply chains end to end has been a challenge for organizations the world...

Aligning Cyber Skills To The MITRE ATT&CK Framework
The MITRE ATT&CK Framework is a comprehensive matrix of tactics and techniques used by threat hunters,...

Top 4 Pitfalls to Avoid when Deploying Office 365
There's no denying that Office 365 is a big deal. It's a big part of the Microsoft Intelligent Cloud...

Forrester Wave Report
In our 33-criteria evaluation of web application firewall (WAF) vendors, we identified the 10 most significant...
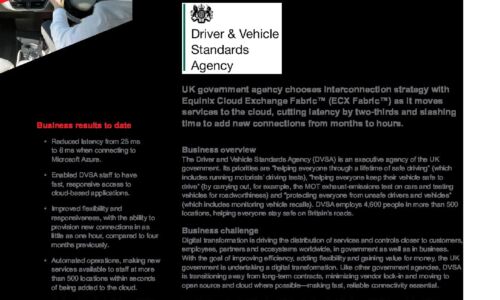
Digital Transformation in the Cloud Drives Government Efficiency
UK government agency chooses interconnection strategy with Equinix Cloud Exchange Fabric™ (ECX Fabric™)...
Unlock the Power of Hybrid Cloud with Consistent Operations
Hybrid cloud creates new possibilities for IT organisations, opening the door to cost-effective scalability,...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.






