AIM
Advanced Email Security
Email is a fundamental feature of modern business. Yet it is also the number one threat vector. Email...

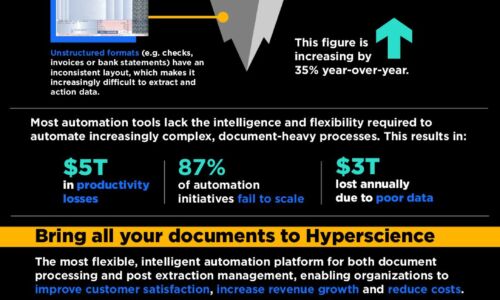
4 steps to optimize your organization to accelerate transformation
Enterprises are working to create a digital foundation for process standardization and automation while...
CMMC Compliance Guide
On January 1, 2020, the United States Department of Defense (DoD) released its Cybersecurity Maturity...

OWASP Top 10
The nonprofit Open Web Application Security Project (OWASP) works to improve the security of software,...
Data-Empowered Construction
In today's construction industry, data analytics is essential for maximizing performance and staying...

Top 10 Active Directory Security Reports and Alerts You Need
Traditional perimeter defense is simply no longer good enough. Today, identity is the new perimeter —...
Social Engineering Handbook: How to Take the Right Action
The aim of this handbook is to help introduce social engineering and its risks to every employee in the...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.