Private Networks

Manufacturers get industrial strength security with private 5G.
5G technology has quickly evolved from aspirational to businessready, and many organizations are already...

Edging Towards SASE: Next generation networking, cloud and security
The global pandemic has delivered a paradigm shift in the relationship between employees and their workplace. The...
Reinventing work How leading
We're coming off one of the most challenging years in business history. The pandemic forced every company...

An Authentication Authority at Your Fingertips: PingFederate
Having an authentication authority within your infrastructure allows you to have a single source of truth...

Tanium Insights: It's Time to Ditch the VPN for Zero Trust
Many organizations have started adopting zero trust strategies to protect their distributed networks...
Trusted Access Report
As global conflicts spill into the digital realm, protecting people through to the enterprise is increasingly...

Introduction to AWS Security
Raise your security posture with AWS infrastructure and services. AWS's approach to security, including...
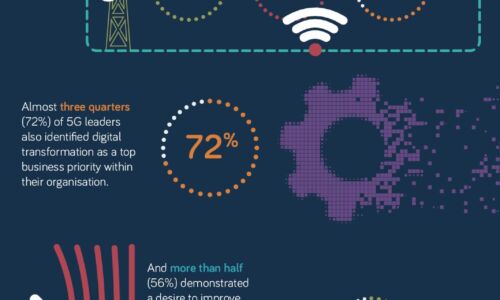
What makes a 5G Leader?
With 5G a still nascent technology, opportunity remains for businesses to accelerate adoption of this...
5G for the enterprise
With a desire to better understand the current, on-the-ground reality for enterprises and organisations...

2022 Threat Report
The BlackBerry 2022 Threat Report is not a simple retrospective of the cyberattacks of 2021. It is a...

Your Path to Zero Trust
In a business world without perimeters and dominated by remote work, finding a balance between easy collaboration...
Getting Started with SASE
Secure Access Service Edge: A guide to secure and streamline your network infrastructure As enterprises...

The State of Zero Trust Report
The zero-trust network security model has become a pervasive topic for IT professionals. Many organizations...
- 1
- 2
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.





