Private Networks

Manufacturers get industrial strength security with private 5G.
5G technology has quickly evolved from aspirational to businessready, and many organizations are already...

Two-Factor Authentication Evaluation Guide
In this guide, you will learn how to evaluate a solution based on: ...

Securely Work From Anywhere With the Fortinet Security Fabric
The way people work has fundamentally evolved, and organizations need to be able to keep workers productive...
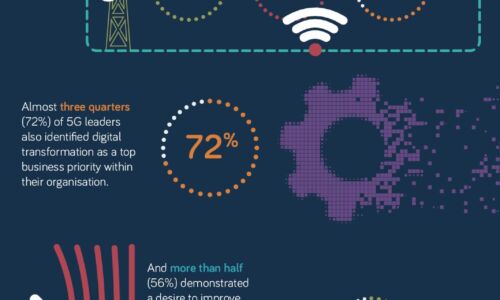
What makes a 5G Leader?
With 5G a still nascent technology, opportunity remains for businesses to accelerate adoption of this...

Global Threat Landscape Report
Another half-year through unprecedented times has passed. But as unique as these times may feel, we continue...

Microsoft Digital Defense Report
Over the past year the world has borne witness to a burgeoning cybercrime economy and the rapid rise...
Zero Trust Access for Dummies
As businesses continue to embrace digital innovation, cloud applications, and the new work-from-anywhere...
Reinventing work - New imperatives for the future of working
Following one of the most challenging years in business history, the pandemic has forced every company...
5G for the enterprise
With a desire to better understand the current, on-the-ground reality for enterprises and organisations...
Hybrid Work Drives the Need for ZTNA 2.0
The COVID-19 pandemic has had a profound effect on the world. Businesses have compressed into months...

Don't Diverge—Converge
Digital acceleration is driving the adoption of hybrid IT architectures. These new hybrid environments...

Reinventing work
We're coming off one of the most challenging years in business history. The pandemic forced every company...
- 1
- 2
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.






