ERP
10 ways voice will disrupt the workplace in the next 5 years
The way businesses adapted to COVID-19 was nothing short of remarkable. Entire companies shifted from...

Optimal Workload Placement for Public, Hybrid, and Private Clouds
The needs and goals of every organization and industry differ, making it impossible to adopt a one-size-fits-all...
The State of Application Modernisation and Hybrid Cloud Computing
Applications are the heart of digital business. Because organisations recognise this reality, they are...

Accelerate your Innovation Strategy with Mulitcloud
Innovation is key to enterprise growth. Businesses that are continually able to add value to existing...
Measuring Cyber Security Culture
It's clear, and it has been for a long time, that traditional tickbox security awareness training efforts...

A Six-Step Guide To Incident Response Planning
You know you need an incident response plan. But creating one can be a daunting, time-consuming task. Where...

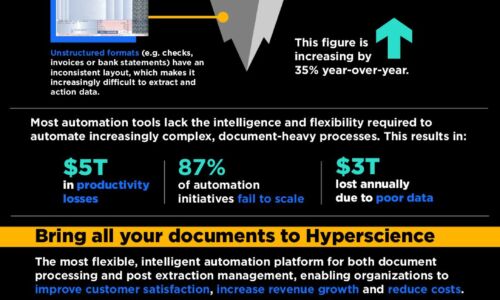
Aberdeen Customer Operations
This report by Aberdeen reveals the role and impact of customer operations on service and back-office...
Clever Energy
Rising emission targets, unpredictable energy usage, and the size and complexity of enterprise operations...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.