Reimagining IT service delivery and operations in unimagined times
Discover the top 3 ways adding Operation Management to your ITSM strategy can help your business be more...
How to Stop Business Email Compromise Threats
While staggering ransomware demands tend to hog the headlines, Business Email Compromise (BEC) is one...
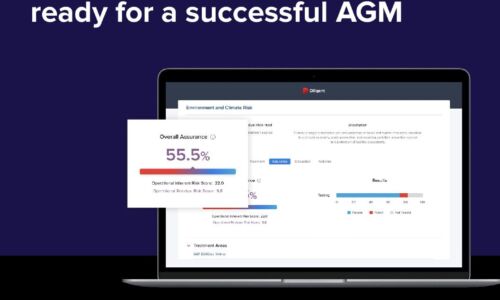
4 tips to ensure your board is ready for a successful AGM
The 2022 AGM season is on course to see unprecedented levels of challenge for boards and businesses....

Optimizing Workload Placement in Your Hybrid Cloud
Many IT organizations are in the process of modernizing their infrastructure, as part of either a digital...
Next-Gen Cloud Contact Centers RingCentral Special Edition
Finally, it's here—the new Next-Gen Cloud Contact Centers for Dummies®, RingCentral Special Edition...

Essential Operational Resilience
COVID-19's far-reaching impacts have thrashed many companies' Plan-A strategies, yet the pandemic offers...
Know Your Options Before Moving To The Cloud
It's imperative for company and IT leaders to understand that the term 'cloud' is very broad and can...

The Total Economic Impact™ Of The CB Predictive Security Cloud
Your endpoints are one of the most targeted assets in your organisation. In 2017 alone, more than 50%...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.