Cloud
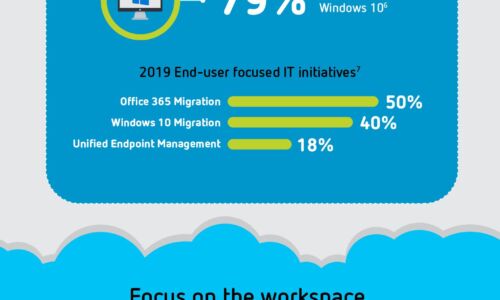
Digital Transformation: A Look Ahead
Digital transformation is reshaping organizations into digital businesses. Organizations are focused...

Is Your WAF Keeping Pace with Today's Advanced Threats eBook
As the threat landscape evolves, so must our security controls and countermeasures. Recent research from...
Responding to Crisis: A Public Sector Guide to continuity planning
Before the start of the COVID pandemic, the capabilities of cloud computing and ERP platforms were already...
Aruba ESP (Edge Services Platform) - Harnessing the Power of the Edge
Every decade or so, we've seen the technology market undergo major shifts. Over the past few decades,...

Making all the Right Connections
Using digital workflows to blast through barriers, drive loyalty, and accelerate growth. Organizations...

20 Examples of Smart Cloud Security
Smart cloud security provides critical capabilities such as governing access and activities in sanctioned...
4 Steps to Establish an Employee Experience Platform
As employees continue to work from anywhere, they expect their workplace to up-level through technology...
Five Best Practices for Mitigating DDoS Attacks
Distributed denial-of-service (DDoS) attacks remain one of the most effective methods used by cybercriminals...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.