Cloud Applications

Delivering Fast and Secure Enterprise Applications
Adopting a zero trust security model — authenticating and authorizing every request, device, and user...

Choosing the Right Cloud Provider for your Business
As cloud computing becomes an increasingly important part of any IT organization's delivery model, assessing...

Valoir Report: Third-Party Support Goes Mainstream
Adoption of third-party support for enterprise software is now mainstream. In a report sponsored by Rimini...

Network Security Approaches and the Case for Zero Trust
Top executives say that legacy network technical baggage is holding them back from transforming their...

Securing high tech industry network data
We all understand the negative impact of data loss, so why is it that so many organisations seem to be...
The Perfect Storm: Why MDR is Your Only Option in Modern Cybersecurity
Covid, work from home, and bring-your-own-device have expanded our threat envelopes 1000X. Attacks with...

Migrating Apps to the Cloud in 5 Steps
Cloud applications, platforms and services are changing the way enterprises compete for customers. The...
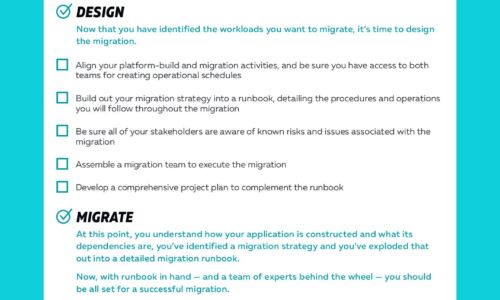
Cloud Migrations Checklist
Cloud migrations can be complex. The key to a successful migration lies in the planning. To help, we've...

Step-by-step Cloud Evolution with Microsoft Azure
IT transformation is more than a one-time migration of applications to the cloud, it's an ongoing process...
Multi-Factor Authentication Guide to On-Premise MFA
Despite the advantages of moving to the cloud and in spite of security assurances, there are still organisations...
Progressive CIOs: driving finance transformation
A successful finance transformation requires several ingredients: vision, agility, and the right system...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.







